Aug 2021
16 Mon
17 Tue
18 Wed
19 Thu
20 Fri 02:00 PM – 05:10 PM IST
21 Sat
22 Sun
Aug 2021
16 Mon
17 Tue
18 Wed
19 Thu
20 Fri 02:00 PM – 05:10 PM IST
21 Sat
22 Sun
Pinned update
Update about videos This update is for participants only
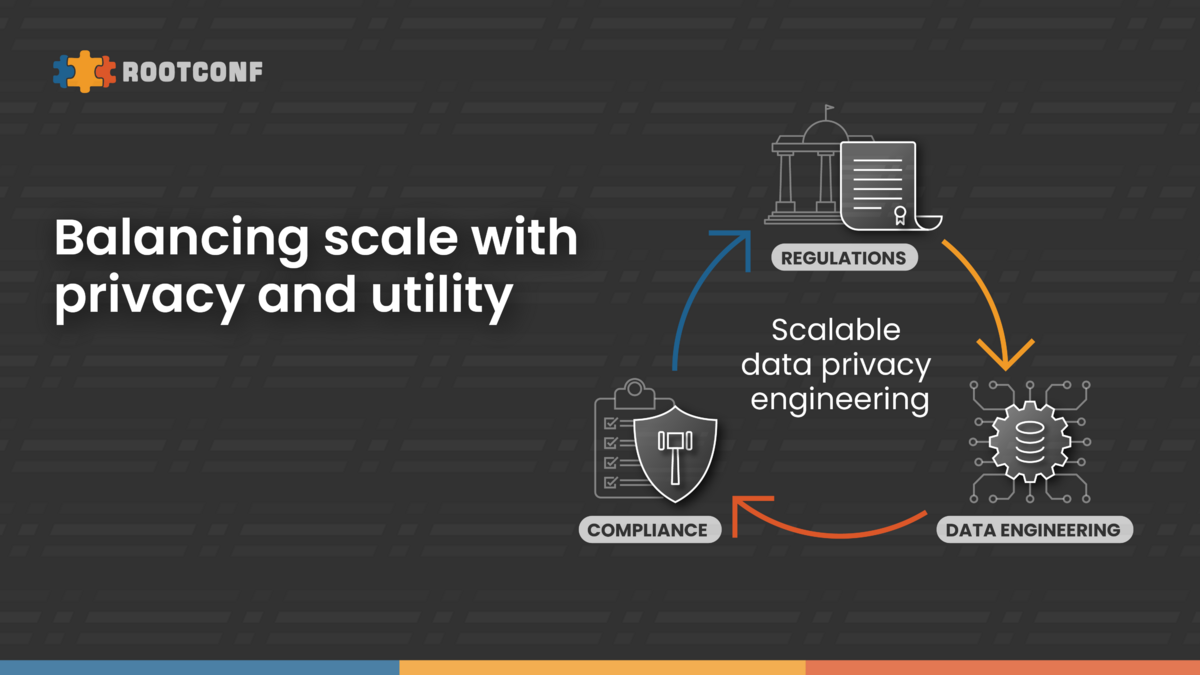
GDPR regulations mandate any data processor - that handles user data - must provide two core functions:
However, both these mandates are not easy for a data processor to comply with because they require the processor to have robust data management practices from day one of their operations. Making a company GDPR-compliant retrospectively is very hard since architects typically focus on designing for scalability, maintainability and data security in the early stages of a company.
We invite talks from practitioners who have gone through the journey of data engineering and how they have managed to balance the difficult goals of privacy, utility and scale within their organizations.
Who should participate:
Schedule: https://hasgeek.com/rootconf/scalable-data-privacy-engineering-conf/schedule
Contact information: Join the Rootconf Telegram group at https://t.me/rootconf or follow @rootconf on Twitter.
For inquiries, contact Rootconf at rootconf.editorial@hasgeek.com or call 7676332020.
Sreenath S Kamath
09 Apr 2021
Rounak Datta
09 Apr 2021
Bhupendra Jain
01 Jul 2021
24 Jul 2021
Hosted by
Supported by
Promoted