Aug 2021
16 Mon
17 Tue
18 Wed
19 Thu
20 Fri 02:00 PM – 05:10 PM IST
21 Sat
22 Sun
Aug 2021
16 Mon
17 Tue
18 Wed
19 Thu
20 Fri 02:00 PM – 05:10 PM IST
21 Sat
22 Sun
Submitted Jul 24, 2021
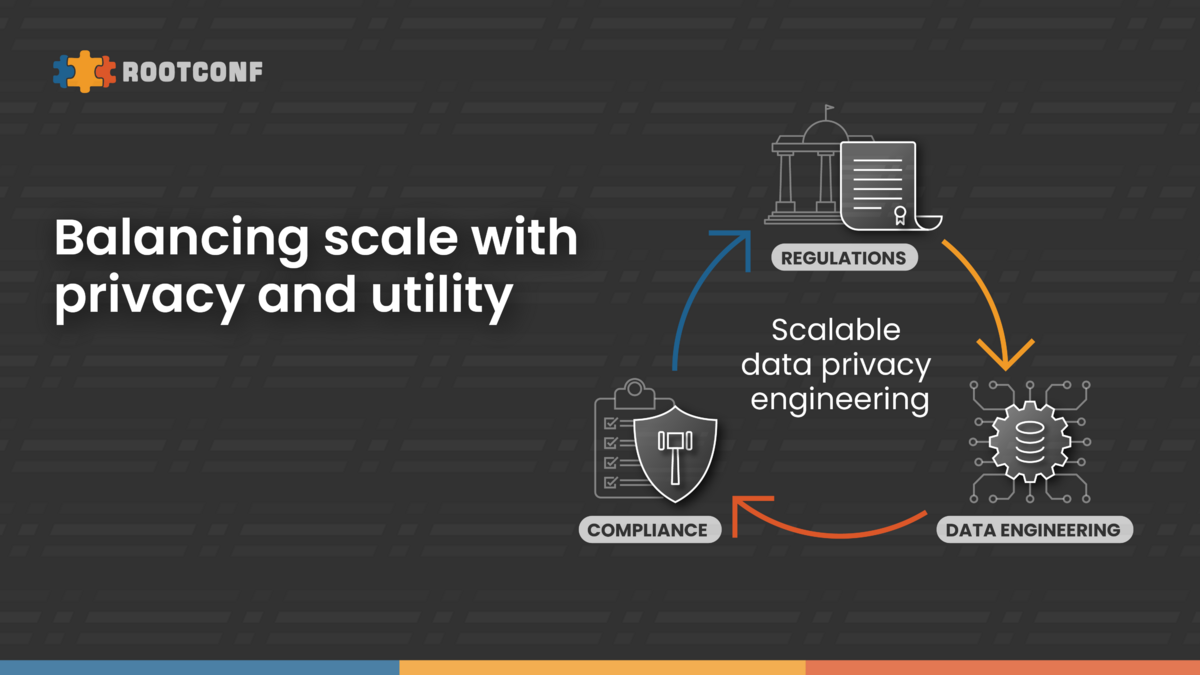
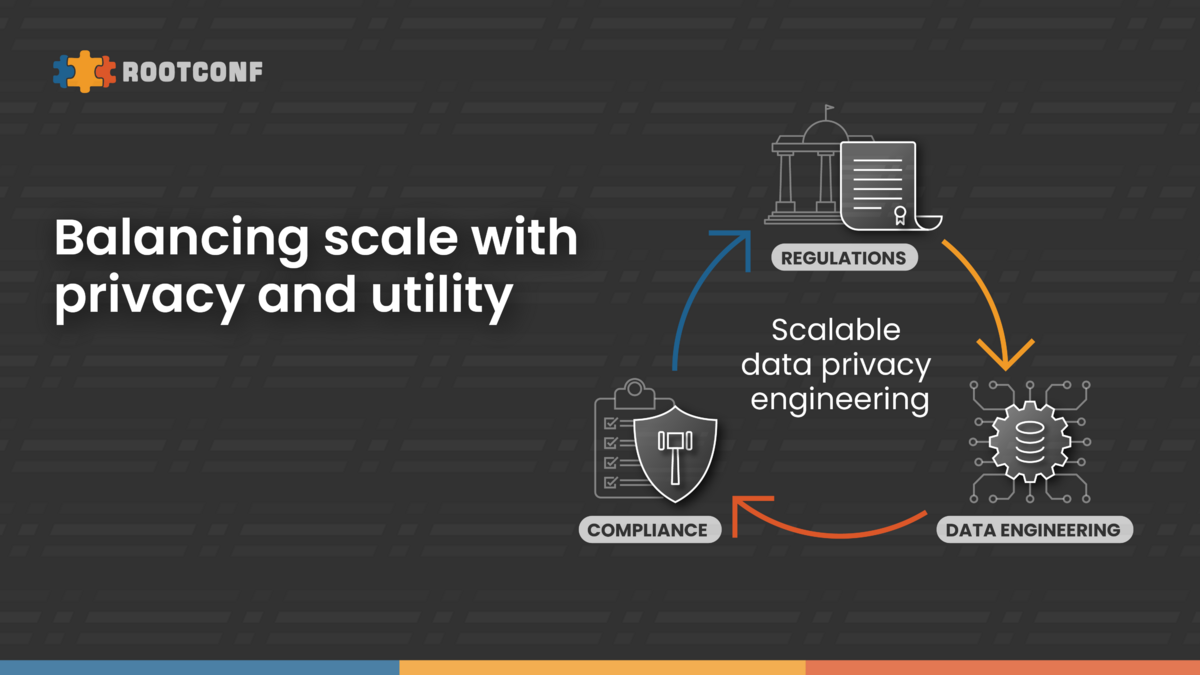
Whether your products and services are B2B or a B2C, you need to be aware of legal requirements that your technological solutions are required and expected to fulfil so that you can design those products and services in accordance with those requirements from the beginning.
Right of Deletion is not absolute. To be able to comply with the requirements for deletion of data, one needs to be aware of the situations in which deletions are necessary under CCPA and GDPR, the timelines within which deletions must take place, and exceptions that permit you to refuse to delete data in certain situations. While dealing with exceptions, it is important to carefully consider what is and what is not permitted, and how to act when taking the benefit of an exemption. One of the exceptions that permits retention of data under GDPR is if you have a legitimate interest that overrides the rights and freedoms of the person whose data is concerned. In one case in Hungary, a person had made a request for deletion of telephone numbers. The company refused to delete that data stating that they have a right to retain it until the debt due from the person to the company is paid off. The Hungarian DPA ruled against the company and held that for legal procedures, it would be sufficient for the company to retain that person’s address, so the company’s justification for retention of telephone numbers is not sufficient, and those numbers must be deleted.
In addition to the above, you need to be aware of all agreements with all service providers and must ensure that measures have been taken to ensure that compliance can take place in the entire chain. For example, if you delete the data within the permitted time limit, but your service provider maintains copies of the data beyond the permitted time limit, then you would be in violation of your legal obligations.
Within an organization, there are multiple roles that must be made aware of these requirements. These include the developers, marketing department, customer service, acquisitions, and legal, as each of them is responsible for separate parts of the overall compliance requirements. The weakest link in compliance is the customer service department as seen from experience.
In this talk, we will discuss the above with regards to the deletion of data under CCPA and GDPR, as well as the outcomes of a few cases that have been decided in EU. Best practices to be implemented.
The right is not limited to users but extends to ex-employees also. Verification of the deletion request is another important aspect.
In India too courts have recognized Right to deletion. Therefore, in coming times this request could from multiple jurisdictons across the globe.
Aug 2021
16 Mon
17 Tue
18 Wed
19 Thu
20 Fri 02:00 PM – 05:10 PM IST
21 Sat
22 Sun
Hosted by
Supported by
Promoted
{{ gettext('Login to leave a comment') }}
{{ gettext('Post a comment…') }}{{ errorMsg }}
{{ gettext('No comments posted yet') }}